In the UK, the government has rolled out the Test and Trace system. According to the website (https://www.gov.uk/government/publications/coronavirus-covid-19-testing-privacy-information/testing-for-coronavirus-privacy-information-quick-read–2) you will be sent a text or email alert with your test result. The results will indicate whether you have Covid-19 and therefore you and your household can take appropriate action.
If you have Covid-19 you will be invited and can voluntarily take antibody tests and donate blood plasma. But fundamentally you will be expected to self-isolate.
So far nothing unusual.
Personal Data
It later mentions who is the data controller (Department of Health and Social Care – DHSC) and mentions the type of details they may need include personal data such as name, date of birth, gender and more. This includes special GDPR type data such as ethnicity too.
The laboratory will analyse your test and your test result will be shared with NPEx, but do not worry, NPEx only have your specimen ID. NPEx will then pass you result to NHS Business Services Authority to inform you of your result.
What they will also do is regularly contact you by phone and text to monitor that you are self-isolating. You have three chances to respond. If you do not, your local authority is informed to investigate. There are some reasonable excuses not to self-isolate.
However, if they feel your excuse is not reasonable and it suggests you are not complying, then your details are then passed to local police forces.
The fine for a criminal offence is £1,000. Repeated offence up to £10,000.
Ready To Sign Up?
So, what impact will this have? For some, this sharing of personal data with police may deter some people from being tested. For some, there a numerous fears that could be put into someone’s mind. How do I get the kids to school? How do I do my food shopping as there are no deliveries? How will the business cope without me? How do I get income to cover my expenses this month?
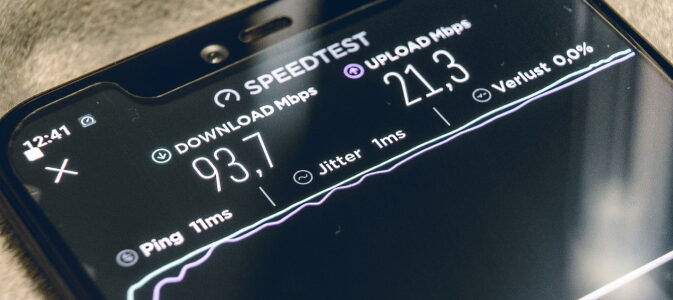
Modern Technology?
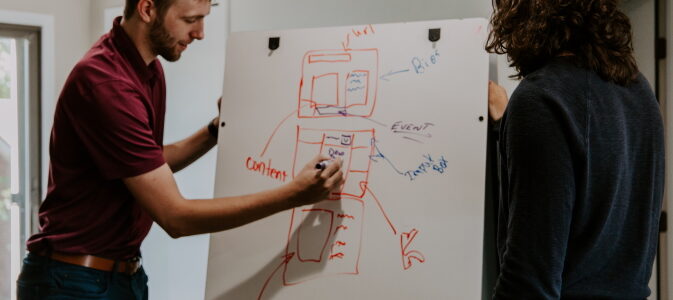
The UK test and trace system was rolled out earlier in this year and had a shaky start. There were reports of test and trace agents sitting around not making calls – I know this is true and I personally know this, as I have seen the training on Zoom and staff with my own eyes. I even helped an individual by buying their headphones and extension network cables (as the service provider did not provide this for work), before a whole of myriad of people were then fired within the first couple of weeks of the Test and Trace system officially “in use”.
Let us not forget the Excel spreadsheet that resulted in 16,000 coronavirus cases being unreported (https://www.bbc.co.uk/news/technology-54423988).
Is using CSV file format really the best way to analyse such results and interchange data in this modern age? I dread to think how they are exchanging our personal data with the Police!
Hope they do better and remember…
Security is not a compromise.